Strava and fitness app leaks
Your morning run starts at your house and ends at your house. Your Strava heatmap publishes that, indexed and searchable. Same for Garmin, Apple Fitness, Peloton, MapMyRun.
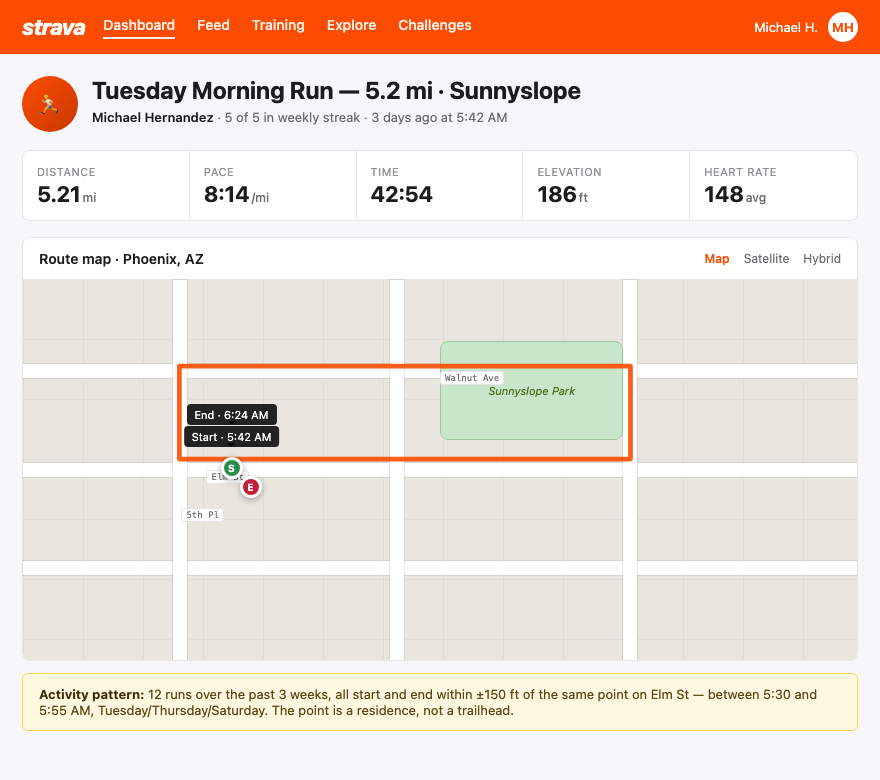
Fitness apps are the highest-resolution location leak available. The 2018 Strava heatmap incident exposed military bases worldwide because soldiers ran loops inside the perimeter. The same mechanic exposes your house every time you run from it. (OSINT is the work of digging up what's public about a person — and a public Strava map is one of the cleanest inputs out there.)
What an adversary sees
Open your public Strava profile in incognito. What's visible:
- Every run plotted on a map. The start point is your driveway. The end point is your driveway. The middle is your neighborhood.
- The heatmap aggregates months of activity into a single image that points to your house like a target.
- Timestamps. "Tuesday 0530, Wednesday 0530, Thursday 0530" tells an adversary exactly when you leave the house and when you come back.
- Vacation rides. The week your activity moves to a different state is the week your house is empty.
- Your friends list. Other runners in your area, often other officers, often with the same exposure.
Garmin Connect, Apple Fitness sharing, Peloton leaderboards, MapMyRun, and Nike Run Club all publish similar data with different defaults. Most users never check.
How to do this on yourself
Open every fitness app you use in an incognito window. Look at what a stranger with no login sees.
- Strava: visit your profile URL without logging in. Click into individual activities. Open your heatmap if you have one.
- Garmin Connect: check your profile privacy and "Activities" sharing setting.
- Apple Fitness: check Settings → Privacy & Security → Health → Sharing.
- Peloton: check leaderboard name and profile visibility.
- MapMyRun, Nike Run Club, Komoot: same drill.
For each app, ask one question: can a stranger see a map that includes my house. If yes, the adversary can see it too.
What to do about what you find
Lock down the location data. The fitness data you can keep.
- Privacy zones around home and work. Strava and Garmin both support hidden-zone settings — pick a radius (Strava allows up to 1km) and the start/end of activities inside that radius gets clipped from the public view. Set one around home, one around work, one around any kid's school you do drop-off runs from.
- Hide individual activities. For sensitive activities — vacations, anything close to the house — set them to "Only You" or "Followers."
- Profile to followers-only. And actually audit who's following.
- Friends list. Hide it. You don't owe anyone a list of who you train with.
- Heatmap. Opt out. In Strava: Settings → Privacy Controls → Aggregated Data Usage → off.
- Repeat the audit every six months. App defaults change. New features ship with permissive defaults.
Your run is your run. The map doesn't have to be anyone else's.
What we handle automatically
We handle the broker layer — the data-broker pages that already publish your home address and tie it to your name. A free scan shows which brokers currently list the address that your Strava map would otherwise point at.
The fitness-app side is on you. No service can flip your Strava privacy zones for you, audit your Garmin sharing, or talk your running buddy into hiding his friends list. The hardening above is the playbook. Run it once, then re-run it every six months.
Most OSINT chains end at a broker page that ties your name to a home address. Run a free scan to see what's currently exposed.