Google yourself
The first thing any adversary does. What they see — broker pages, social profiles, news, court records — and how to read your own results like one.
Google is where almost every search for you starts. The same path a stalker, defendant, or harasser walks ends at your front door. OSINT is the work of digging up what's public about a person — searching, cross-referencing, putting the pieces together. Walk a working pattern and read the results the way the searcher does.
What an adversary sees
Type your full name into Google. The first ten results for a cop, nurse, or firefighter look almost the same:
- Three or four data broker pages with your address, age, relatives, and prior cities
- A Whitepages or TruePeopleSearch entry near the top
- LinkedIn, if you have one tied to your real name
- A local news hit — an arrest you made, a department promotion, a use-of-force story
- Court records if you've been a witness or party in a civil case
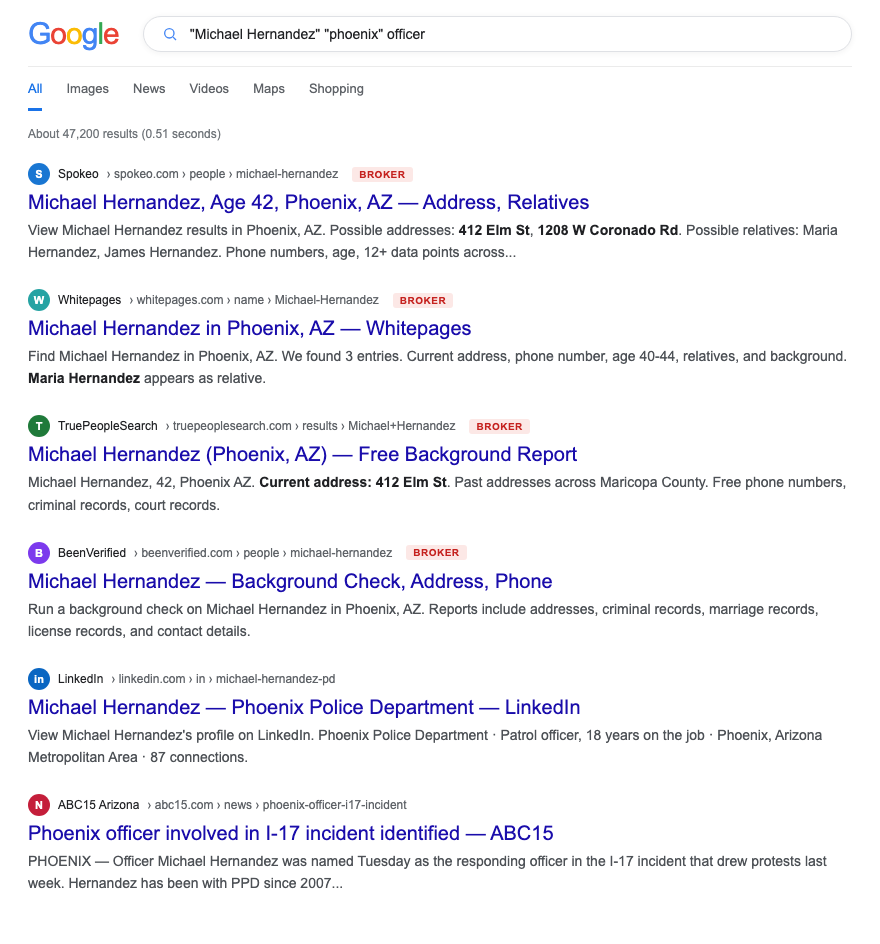
The broker pages are the dangerous ones. News is context. Brokers are address.
How to do this on yourself
Run these searches in order. Use an incognito window so personalized results don't lie to you.
"First Last"— baseline. What does the open web know."First Last" site:linkedin.com— your LinkedIn and anyone who's tagged you."First Last" "department" OR "precinct" OR "sheriff"— surfaces work-tied results fast."First Last" "city, state"— narrows to your jurisdiction. This is what an adversary types."First Last" filetype:pdf— academy rosters, awards lists, court filings, union newsletters.- Google Images for your name — face matches an adversary can run through reverse image search.
Repeat with middle initial and any nicknames you've used publicly. Note every result that ties your name to an address, a workplace, or a family member.
What to do about what you find
Sort results into three buckets and handle each differently.
- Broker pages. Opt out one by one or have us do it. These are the only results that hand over your address. Removing them collapses most of the search-result threat.
- LinkedIn and social. Lock down. Hide connections. Strip the department from the headline if you can. Old photos with a uniform visible — pull them.
- News and court records. You can't remove these. You can make them less useful by killing the broker stack that turns "Officer Smith arrested a guy in 2019" into "Officer Smith lives at 412 Elm."
If you're seeing your home address in the snippet preview without clicking, you have an active problem. Start the doxxing playbook.
What we handle automatically
We handle the broker layer — the part that converts "your name in a Google result" into "your address in a Google result." That's the conversion step every doxxer needs.
A free scan shows you exactly which broker pages are surfacing for your name today, ranked by visibility. We file removals across the network and re-check monthly because brokers re-publish.
The LinkedIn lockdown, the old-account scrub, the family-member conversation — those stay on you. We give you the playbooks. See scrubbing old social media and family member OSINT leaks for the rest.
Most OSINT chains end at a broker page that ties your name to a home address. Run a free scan to see what's currently exposed.