Social engineering defense
OSINT enables better social engineering. The more an adversary knows about you — kids' names, partner's job, prior addresses — the more convincing the call, email, or in-person pretext becomes.
OSINT — the work of digging up what's public about a person — is the input. Social engineering is the output. The defense covers both: reduce what's discoverable, and recognize the pretext when it arrives.
What an adversary sees
A pretext informed by good research doesn't sound like a scam. It sounds like a person who already knows you. Real patterns:
- A call to your desk: "Hey, this is Mike from the alarm company — your sister Sarah said you'd be the right person to confirm the upgrade at 412 Elm." Sister's name and address from a broker page. Alarm company guessed from the neighborhood.
- A text to your spouse: "It's Officer Davis from your husband's unit, he was in a minor crash, can you confirm the home address for the report." Unit name from a department roster, husband's name from anywhere.
- An email referencing your kid by name and school: "Coach asked me to forward this to all the parents on the U10 team." Kid's name and team from a social-media post. Parents' email from a broker.
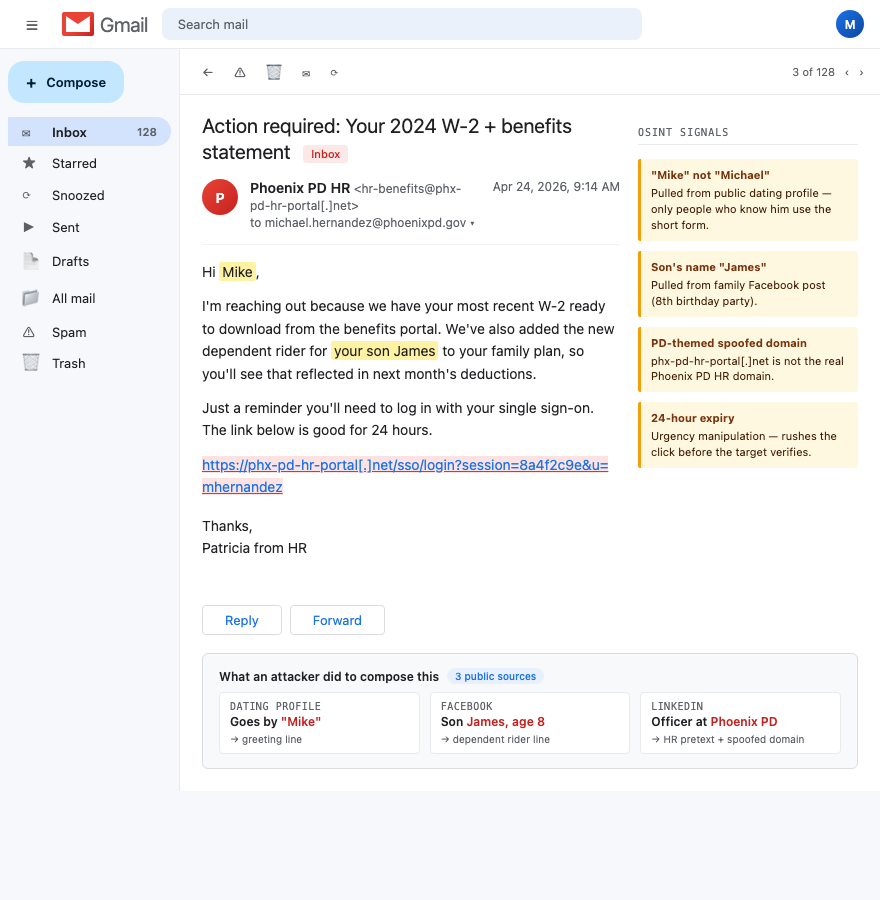
The detail is what gets through. Generic phishing fails. Specific phishing — with a real name, a real relationship, a real address — gets answered.
How to do this on yourself
Build the attacker's dossier on yourself. Then write the pretext.
- Run your name through three brokers: Spokeo, Whitepages, USPhoneBook. Print every page.
- Add what's on your spouse's and kids' social media. School name, team name, dog's name, vacation spots.
- Add what's on your LinkedIn. Department, unit, years on, prior agencies.
- Now write three pretexts an adversary could use against you, your spouse, your kid, your parents. Be specific. Use the real names and the real addresses.
The exercise is uncomfortable. That's the point. Once you've written the convincing version, you'll recognize it when it arrives.
What to do about what you find
Defense is family-wide and protocol-based, not individual.
- Verify-out-of-band rule. Any call, text, or email asking for information, money, or access — hang up and call back on a known number. Always. No exceptions for "I'm in a hurry."
- Family code word. A short word the whole household knows. Anyone calling claiming to be a family member or speaking on their behalf has to give it. Kids included.
- Refusal-to-share defaults. At work HR and finance, never confirm a home address or family detail by phone. The pretext call to your HR department is the most common path in.
- Train your spouse and kids on the patterns. Walk them through the three pretexts you wrote. Tell them what a real call from your unit sounds like and what a fake one sounds like.
- Caller ID is a lie. Spoofing is trivial. Treat the number on the screen as suggestive, not authoritative.
What we handle automatically
We handle the input layer — the broker pages that hand an adversary the names, addresses, and relationships they use to build a convincing pretext. Cleaning the broker network shrinks the dossier they can build on you in an hour of Googling.
The recognition side is operational and on you and your family. We can't answer your spouse's phone or train your kid to use the code word. We give you the framework; you run it at home.
Run a free scan to see what an adversary can pull together on you right now. That's the raw material for every pretext aimed at you. See also family-OSINT leaks for the family-side cleanup.
Most OSINT chains end at a broker page that ties your name to a home address. Run a free scan to see what's currently exposed.