Your car's OSINT footprint
Make, model, color, bumper stickers, dealership decals, roof rack — all narrow the field for someone trying to identify your vehicle. The plate is one input among many.
Vehicle identification runs broader than plate lookups alone. OSINT is the work of digging up what's public about a person — searching, cross-referencing, putting the pieces together. Your car carries plenty of it. The vehicle's appearance lets an adversary identify your car at any location, even without a clear plate read. Once identified, following from work to home is operationally trivial.
What an adversary sees
An analyst with one clear photo of your vehicle in a parking lot has more than you think:
- Year, make, model, trim, color — narrows the registration set in your county to a few hundred vehicles
- Bumper stickers — FOP (police union), PBA (police benevolent association), "Back the Badge," union local decals, military veteran plates, kid's school stickers all flag affiliation and family
- Dealership decals on the trunk or license-plate frame — tells them which dealer = which neighborhood you bought in
- Roof rack, trailer hitch, ski box, bike rack — narrows further by lifestyle and by where you'd realistically park
- Window stickers — gym membership, parking permits with lot numbers, gate codes, base access decals
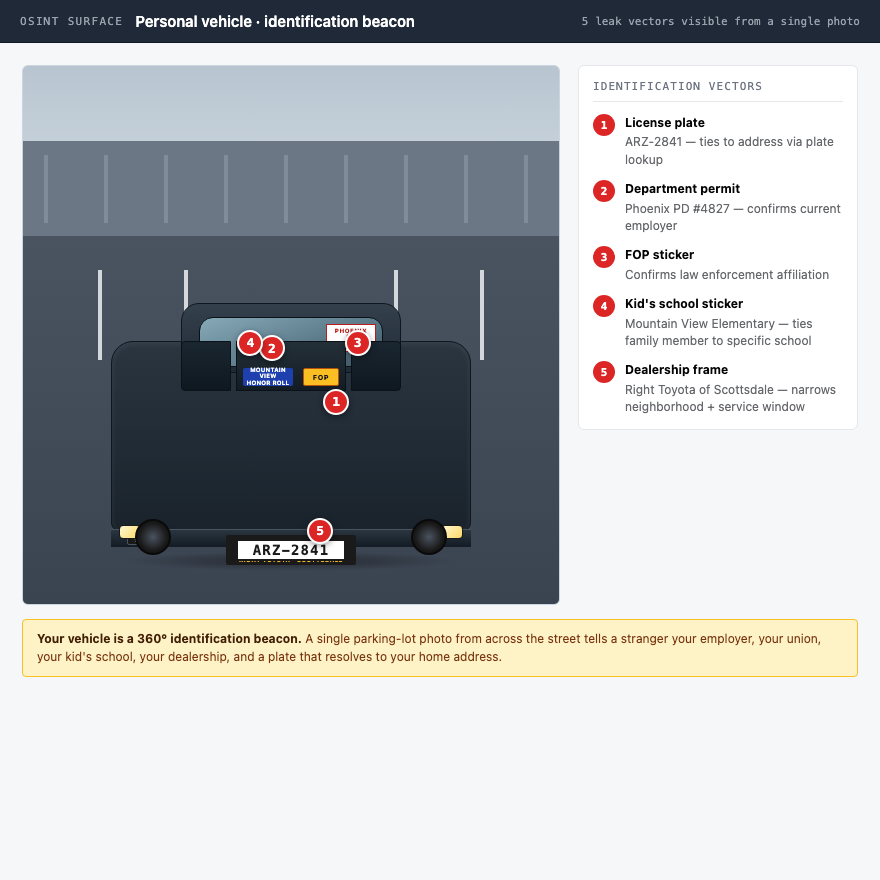
Once your vehicle is identifiable on sight, an adversary doesn't need the plate. They wait at the precinct lot, follow at a distance, and have your home address by dinner.
How to do this on yourself
Walk around your personal vehicle with a notepad. Inventory every identifying detail an adversary could spot from twenty feet away.
- Front, rear, both sides, top — note every sticker, decal, frame, and aftermarket part
- Photograph the way a stalker would — from across a parking lot, with a long lens
- Run your plate against the lookup tools listed in license-plate OSINT
- Check Google Street View for your home address — your vehicle may already be photographed in your driveway
- Search your plate as text on Reddit, Facebook Marketplace, and dashcam YouTube channels
Then do the same for your spouse's car. The family vehicle parked at your house is a second identifier pointing at the same address.
What to do about what you find
Strip everything that announces who you are or what you do.
- No occupation-affiliated stickers on the personal vehicle. No FOP, no PBA, no union decals, no "Back the Badge." Show support on the work vehicle or not at all.
- No specialty plates that announce the job. Standard-issue plates only. Vanity plates with badge numbers, unit names, or department callsigns come off.
- Dealership decals removed. Peel them. Most come off with a hairdryer and a plastic scraper.
- Vary parking spots if your work setup allows. Same spot every day at the same time builds a pattern that anyone watching can read in a week.
- Garage the vehicle at home if possible. Street View and a drive-by can't catalog what's behind a closed door.
Your spouse and kids' vehicles get the same treatment. School decals on the back window tell a stalker which school to wait outside of.
What we handle automatically
Vehicle OSINT is mostly operational — the stuff your spouse sees you peeling off the bumper this weekend. We can't do that part for you.
What we do handle: the broker-side address lookup that the plate-to-name conversion ends at. Once an adversary has identified your vehicle and pulled the plate, they need a current home address to act on it. That's the layer we clean.
See license-plate OSINT for the plate-lookup side, and run a free scan to see which brokers currently tie your name to a home address. Cleaning the broker layer means the plate read leads to a dead end.
Most OSINT chains end at a broker page that ties your name to a home address. Run a free scan to see what's currently exposed.